Certificate file extensions are confusing: .pem, .crt, .cer, .der, .key, .csr—what's the difference? The truth is, extensions are often misleading. What matters is the encoding (PEM vs DER) and content type (certificate vs key). This guide clarifies everything.
The Two Core Encodings
All certificate files use one of two encodings:
1. PEM (Privacy-Enhanced Mail)
Format: Base64-encoded text with header/footer
-----BEGIN CERTIFICATE-----
MIIFazCCBFOgAwIBAgISA+goLKPvWE... (Base64 text)
-----END CERTIFICATE-----Characteristics:
- ✅ Human-readable (you can open in text editor)
- ✅ Email/copy-paste safe (ASCII characters only)
- ✅ Can contain multiple certificates (chain)
- ✅ Can mix certificates and keys in one file
Common extensions: .pem, .crt, .cer, .key, .csr
2. DER (Distinguished Encoding Rules)
Format: Binary (raw ASN.1 structure)
Characteristics:
- ❌ Not human-readable (binary data)
- ✅ Smaller file size (~25% smaller than PEM)
- ❌ Typically one certificate per file
- ✅ Native format for Java, Windows
Common extensions: .der, .cer (yes, .cer can be either!)
File Extensions Don't Determine Format
The confusing truth: Extensions are just conventions. A .crt file might be PEM or DER. A .cer file could be either. You must check the content.
| Extension | Common Encoding | Contents | Typical Use |
|---|---|---|---|
| .pem | PEM | Cert, key, CSR, chain | Linux (Apache, Nginx) |
| .crt | PEM (usually) | Certificate only | Apache, Nginx |
| .cer | DER or PEM | Certificate only | Windows, Java |
| .der | DER | Certificate or key | Java, Windows |
| .key | PEM | Private key | Apache, Nginx |
| .csr | PEM | Certificate signing request | All platforms |
| .pfx/.p12 | PKCS#12 (binary) | Bundle (cert+key+chain) | IIS, Windows |
How to Identify the Format
Method 1: Open in Text Editor
If you see:
-----BEGIN CERTIFICATE-----→ It's PEM (regardless of extension)
If you see: Random binary characters (question marks, symbols, gibberish)
→ It's DER or PKCS#12
Method 2: OpenSSL Commands
Check PEM certificate:
openssl x509 -in cert.crt -text -noout✅ Success = PEM format
Check DER certificate:
openssl x509 -in cert.cer -inform DER -text -noout✅ Success = DER format
Method 3: File Command (Linux/Mac)
file cert.crt
# Output: "PEM certificate" or "DER certificate"What Each Server Needs
Apache HTTP Server
Required format: PEM
# httpd.conf or ssl.conf
SSLCertificateFile /path/to/cert.crt # Your certificate (PEM)
SSLCertificateKeyFile /path/to/private.key # Private key (PEM)
SSLCertificateChainFile /path/to/chain.pem # Intermediate certs (PEM)Nginx
Required format: PEM (combined chain)
# nginx.conf
ssl_certificate /path/to/fullchain.pem; # Cert + intermediate (PEM)
ssl_certificate_key /path/to/private.key; # Private key (PEM)Note: Nginx wants cert + intermediate in one file (fullchain.pem).
Microsoft IIS
Required format: PFX (PKCS#12)
Import via IIS Manager or PowerShell. See our PEM to PFX guide.
Java/Tomcat
Required format: JKS, PKCS#12, or sometimes DER
# Convert PEM to PKCS#12 for Java
openssl pkcs12 -export -in cert.crt -inkey private.key -out keystore.p12 -name tomcat
# Import to JKS (Java KeyStore)
keytool -importkeystore -srckeystore keystore.p12 -srcstoretype PKCS12 -destkeystore keystore.jks -deststoretype JKSmacOS Keychain
Accepts: PEM, DER, PFX/P12
Double-click any cert file to import, or use Keychain Access app.
Windows Certificate Store
Prefers: DER (.cer) or PFX (.pfx)
Double-click to install, or use certutil -importpfx.
Conversion Cheat Sheet
PEM → DER
openssl x509 -in cert.crt -outform DER -out cert.derDER → PEM
openssl x509 -in cert.der -inform DER -out cert.pemPEM → PFX (with key and chain)
openssl pkcs12 -export -out certificate.pfx -inkey private.key -in cert.pem -certfile chain.pemPFX → PEM (extract all)
# Extract certificate
openssl pkcs12 -in cert.pfx -clcerts -nokeys -out cert.pem
# Extract private key
openssl pkcs12 -in cert.pfx -nocerts -nodes -out private.key
# Extract chain
openssl pkcs12 -in cert.pfx -cacerts -nokeys -out chain.pemCombine Separate Files into Fullchain (for Nginx)
cat cert.crt intermediate.crt root.crt > fullchain.pemCommon Mistakes and How to Avoid Them
Mistake 1: Using .crt Extension for DER Format
❌ Wrong: Save DER as cert.crt and use in Apache
✅ Correct: Convert DER → PEM first, or use cert.der extension
Mistake 2: Including Private Key in Certificate File
❌ Insecure: Combining key and cert in one file for Apache (cert.pem contains both)
✅ Correct: Keep separate (cert.crt + private.key), restrict key permissions (chmod 600)
Mistake 3: Forgetting the Intermediate Certificate
Symptom: "Certificate chain incomplete" error
✅ Fix: Always configure SSLCertificateChainFile (Apache) or combine into fullchain.pem (Nginx)
Mistake 4: Wrong File Order in Chain
❌ Wrong order: Root → Intermediate → Your cert
✅ Correct order: Your cert → Intermediate → Root
PEM Variants: Understanding the Headers
Certificate
-----BEGIN CERTIFICATE-----Private Key (PKCS#1)
-----BEGIN RSA PRIVATE KEY-----Private Key (PKCS#8 Encrypted)
-----BEGIN ENCRYPTED PRIVATE KEY-----Private Key (PKCS#8 Unencrypted)
-----BEGIN PRIVATE KEY-----Certificate Signing Request (CSR)
-----BEGIN CERTIFICATE REQUEST-----Public Key
-----BEGIN PUBLIC KEY-----Conversion example (PKCS#1 → PKCS#8):
openssl pkcs8 -topk8 -inform PEM -outform PEM -in rsa_private.key -out pkcs8_private.key -nocryptSecurity Considerations
PEM Files (Text)
- ✅ Easy to inspect and verify
- ⚠️ Can be accidentally committed to version control (use
.gitignore) - ⚠️ Private keys readable if file permissions wrong (
chmod 600)
DER Files (Binary)
- ✅ Harder to accidentally expose in logs/error messages
- ❌ Harder to inspect (need OpenSSL commands)
- ✅ Slightly smaller file size
Best Practices
- Restrict private key permissions:
chmod 600 private.key(Linux) or ACL (Windows) - Never commit keys to Git: Add to
.gitignore - Use password-protected keys in transit: Encrypt with OpenSSL
- Verify certificates after conversion:
openssl x509 -text -noout -in cert.pem
FAQ: Certificate Format Questions
Can I rename .crt to .pem?
Yes, if it's already PEM-encoded (check with text editor). Extensions are just conventions—format matters, not filename.
Why do certificate providers give me multiple files?
Typical download: yoursite.crt (your cert), intermediate.crt (intermediate CA), root.crt (root CA). Apache needs all three. Nginx wants them combined into one file.
What's a "certificate bundle" or "fullchain"?
Your certificate + intermediate + root CA combined in one PEM file, in that order. Required for Nginx, optional for Apache.
Can I convert PEM to DER and back without losing data?
Yes—conversion is lossless. The underlying X.509 certificate data is identical, only the encoding changes.
Why does my .cer file not work in Apache?
It's probably DER-encoded (Windows default). Convert to PEM: openssl x509 -in cert.cer -inform DER -out cert.pem
Related Guides
- PEM to PFX — For Windows/IIS deployment
- PFX to PEM — Reverse conversion
- CRT to PEM — Certificate conversion
- DER to PEM — Binary to text conversion
Conclusion
Certificate format confusion stems from misleading file extensions and two different encodings (PEM vs DER). Remember: PEM is Base64 text with headers (for Linux/Apache/Nginx), DER is binary (for Windows/Java). Extensions like .crt, .cer, and .pem are just conventions—always verify the format by inspecting the content. Use OpenSSL for conversions, combine certificates correctly for chains, and always keep private keys secure with proper permissions. Whether deploying on Apache, Nginx, IIS, or Tomcat, understanding these format differences ensures smooth SSL/TLS certificate installation without errors.
Related Articles
- PEM to PFX (2026): Windows IIS Certificate Deployment - Practical conversion example using these formats
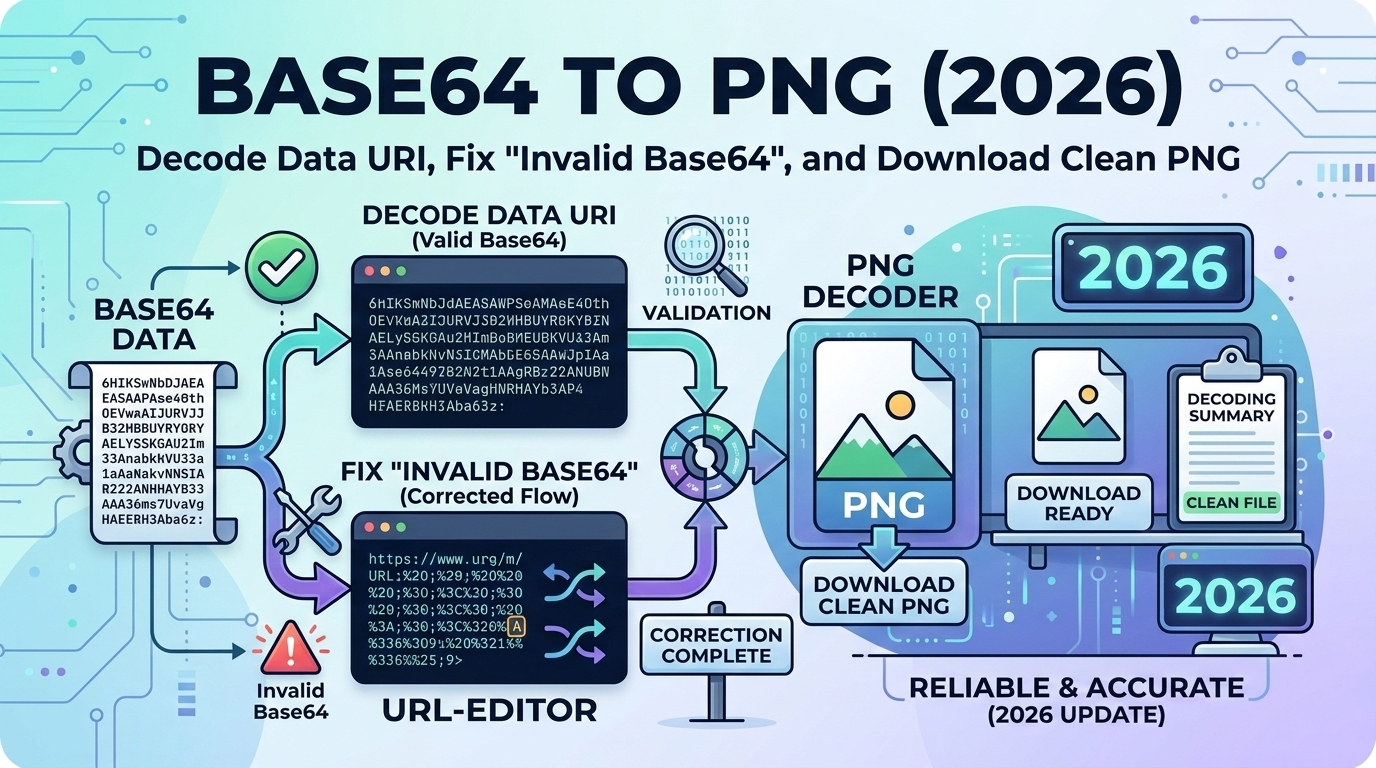
- Base64 to PNG (2026): Decode Data URI Images - Understanding Base64 encoding used in PEM
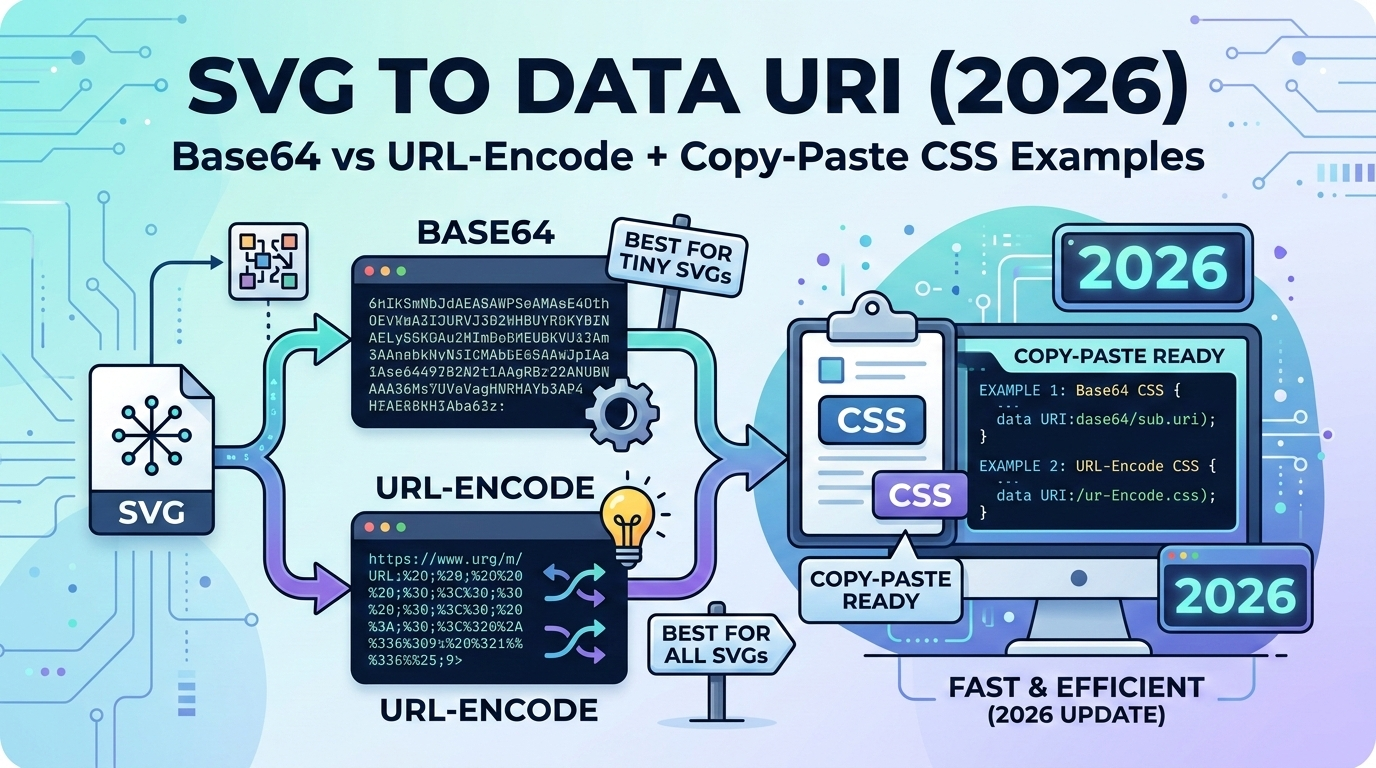
- SVG to Data URI (2026): Base64 Web Graphics - Another Base64 encoding use case